www.industry-asia-pacific.com
19
'22
Written on Modified on
Yokogawa News
Yokogawa Launches OpreX IT/OT Security Operations Center Service
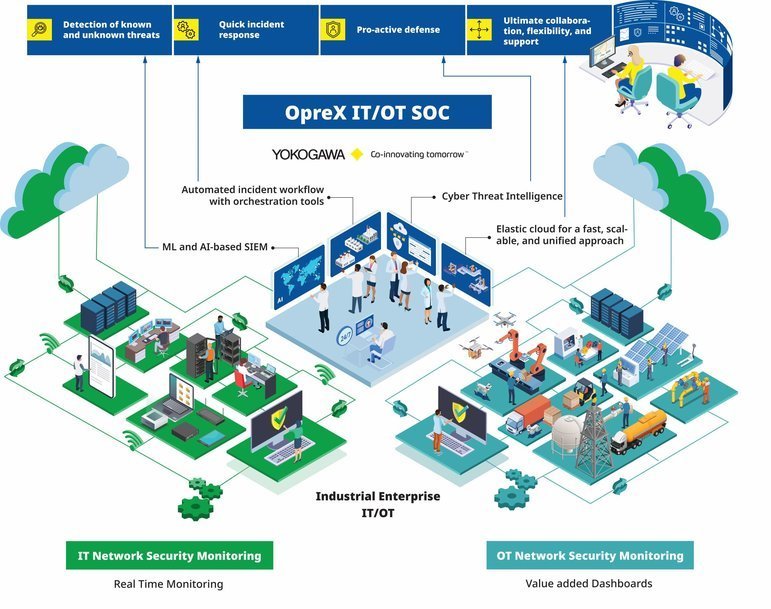
Yokogawa Electric Corporation announces the release on this date of the OpreXTM IT/OT Security Operations Center (IT/OT SOC) service. This new addition to the OpreX Safety and Security family is a centrally managed service based on people (service organization), processes, and technology. Targeted primarily at industrial enterprises, this service was developed by Yokogawa to improve the security of IT and OT networks by detecting, analyzing, and enabling a quick and effective response to cybersecurity incidents from anywhere in the world.
Providing enterprise IT/OT assets with real-time protection from cybersecurity threats.
Monitoring in real-time for cybersecurity threats to networks and IT/OT infrastructure offers customers comprehensive protection that mitigates both operational and business downtime and eases the task of IT/OT asset management.
Development Background
New cybersecurity threats emerge every day. As technologies evolve, so do the associated cyber threats and vulnerabilities that can cause severe damage to an organization's data, assets, and reputation. Security operations centers (SOCs) are increasingly regarded as critical to an effective cybersecurity strategy as they proactively focus on undiscovered cyber security threats and vulnerabilities.
While traditionally, the IT and OT domains have been managed separately, the convergence of IT and OT networks -- driven by digital transformation (DX) -- has made the two domains increasingly interdependent. For efficiency reasons, organizations can choose to establish a converged IT and OT SOC that acts as one team, using a shared data lake, tooling, resources, and processes.
In 2019, Yokogawa began developing an internal security monitoring service for the IT infrastructure of Yokogawa Group companies around the globe, monitoring personal computers, DNS/AD servers, intrusion detection systems, and factory systems and processing up to 600 million events a day by using cyber threat intelligence (CTI) and machine learning (ML) programs. Utilizing the vast experience that it has gained internally, and complemented by its best-in-class approach to OT security for its customers, Yokogawa has developed a cloud-based IT/OT SOC service to provide its customers with an integrated, consistent, and holistic approach to security for the IT and OT domains.
Features
IT/OT SOC is a security monitoring service that uses next-generation Security Information and Event Management (SIEM) which is fast, scalable, and unified. The service uses various CTI and ML tools to collect event logs from customers' IT/OT devices to detect cyber-attacks, unauthorized accesses, and infiltration by malware. It provides a wide range of analysis, consulting, and managed services with next-generation SOC architecture.
1. Detection of unknown threats by ML and AI-based SIEM
Powered by ML and AI, the IT/OT SOC is an advanced intelligent SIEM service that detects abnormal activities and sophisticated attacks. The ML- and AI-driven SOC can devise a threat response by implementing the right playbook, reducing the investigation time by providing analysts the precise action point, and minimizing the mean time to detect and respond.
2. Reduction of human errors and acceleration of workflow through the use of advanced automation and orchestration tools
IT/OT SOC employs a security orchestration, automation, and response (SOAR) platform of technologies that coordinate, execute, and automate tasks between various people and tools, minimizing human errors and thereby speeding up the overall security response.
3. 24-hour protection through CTI
Collected logs and event information are collated in real-time by multiple CTI tools, providing around-the-clock, year-round protection through the detection of suspicious communications and malware.
4. Ultimate deployment flexibility and support
IT/OT SOC can be integrated with existing IT/OT security services, network security infrastructure, and incident management systems. Customers can also integrate it with their SOCs or Yokogawa's existing SOC.
Major Target Markets
Oil and gas, petrochemicals, chemicals, iron and steel, pulp and paper, electric power, and wastewater treatment
Applications
Information security, network security, application security, IT and OT security monitoring and detection, cybersecurity consulting
www.yokogawa.com

